We’re always nagging our clients, friends, colleagues and pets about improving their online security, especially their passwords. That’s because in our experience most people’s passwords are woefully inadequate. We’ve always been mindful of our own security but after helping someone caught up in a Business Email Compromise scam, we’ve spoken extensively to people who deal with cybercrime on a daily basis: police, banks, IT firms, law societies, victims and counsellors. The following notes are us digesting the information from a lay perspective in the hope that it might be useful beyond our client base.
“You’re only as safe as your weakest link” – it only takes one step in the chain to fail and you could be opening yourself up to being hacked. While the damages from hacking aren’t always serious, they can go up to and including losing your life savings and being legally liable for your customers’ losses.
Below are some tips across 3 areas of security: logins/passwords, email and finances.
Logins/Passwords
- This is a non-secure password: 123456. Apparently 10% of people use passwords from the worst 25 passwords ever list like this one.
- This is also a non-secure password: 304r@rd1ndr1ve. Changing letters into special characters doesn’t help, a program used by a hacker can do the same.
- This is a pretty secure password: QjK4o8eA95CsKXJp0F7Q. We used https://1password.com/password-generator to create this one, just using the default settings is enough to create one that can’t be hacked easily.
Any password you can remember yourself is not secure. Secure passwords are generally gibberish.
If you reuse passwords across websites, a scammer has probably already got your password. Just enter your email address at https://haveibeenpwned.com/ and see which account of yours is known to have been hacked. If you use that password anywhere else, scammers may already have access to that other account.
A lot of people laugh at the idea of the non-internet-savvy person writing their passwords down on a piece of paper that they keep at home, but as long as this system uses secure passwords it’s actually much better than what most people do (non-secure passwords reused across multiple websites). A password-protected spreadsheet to store all your passwords is also fine as long as your master password is a good one. Of course the best solution is to use a password manager, of which there are many, some free but at $50/year 1Password is usually a good investment. Here’s a list of options and a price/feature comparison.
The password to open your password manager should be a good one, we recommend a passphrase because of this XKCD: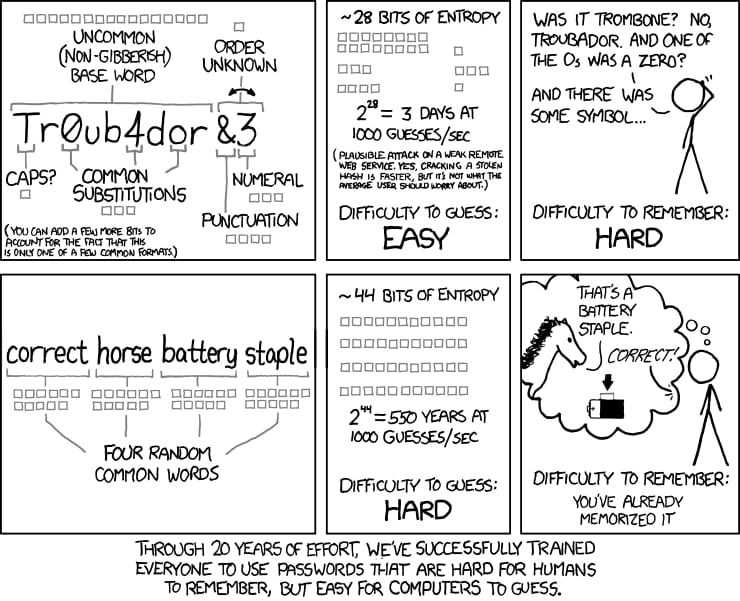
There’s an entire website dedicated to helping you create a passphrase using the XKCD method: correcthorsebatterystaple.net
The hard work comes after you set up your password manager: you will need to migrate all your passwords there AND usually change them to make them secure. Storing insecure passwords in your password manager is pointless.
Also, note that the above (XKCD) method for passwords is only relevant for your password manager’s master passphrase because you’ll have to remember it. For actual passwords to websites you’re better off just using the password manager’s native “generate password” feature to create a long string of gibberish.
In addition to helping secure your passwords, if you only log in using a password manager it will prevent a lot of phishing attacks. Most phishing operates on a domain mismatch. A spammer might not be able to make a fake page on anz.com.au but they can register something like onlinebanking-anz.com and a lot of people won’t notice. But a password manager will know the difference and will not offer to fill out your ANZ password on onlinebanking-anz.com.
Finally you should set up 2 factor authentication for all websites that allow it. Which is a lot by now, you can do a search here. Google’s research shows that setting this up can block up to 100% of automated bots, 99% of bulk phishing attacks, and 66% of targeted attacks.
If your mobile phone suddenly goes into ‘SOS Only’ mode and cannot make or receive calls, this is likely to be because a scammer has impersonated you to get your phone number transferred to them in order to break your 2 factor authentication at some account. Contact your financial institutions immediately and lock your accounts until you’ve confirmed that your number hasn’t been intercepted by scammers.
The account that scammers will be most likely to target is your email. If they can get in (mostly through phishing), they can place bots on your account monitoring conversations for months or even years until an opportunity presents itself (eg. talk of an invoice, credit card details or bank transfer). At this point they can intercept the email, reply impersonating you, send emails to your suppliers and so on.
The scariest part is that you may have already been hacked months ago and not know it.
In almost all cases, if someone is sitting on your account, logging out from all locations and changing your email password is enough to log them out. That’s another reason why you should undertake that migration to the password manager outlined above, as this will likely kick out anyone who might already have access to your account.
We would also recommend not sending any sensitive information via email (eg. passwords, credit card numbers, bank account details). Apps like WhatsApp, Telegram or Signal and other methods like SMS or specialised services like 1ty.me are much more secure.
Finances
Checking the BSB location of the bank details you’ve been provided for a payment is no longer a sufficient security barrier. The scammers today have an extensive network of bank accounts across Australia (60% of which belong to victims of different online scams) and in most cases will nominate an account close to where the real person is expected to be.
We suggest adding verbal confirmations to any substantial financial procedures. Securing the correct phone number at the start of a client/supplier relationship is the key here. Sometimes this can be the only way to identify if a hack has taken place.
Law reform in this area is on its way, but not in place yet. This means liability and best practice when it comes to businesses and clients involved in cybercrime is still quite messy. If you’re a business owner or run a website, you should consider cyber crime insurance. If you get hacked without being negligent, you wouldn’t be covered by standard insurance like professional indemnity. When thinking about the potential financial risk of a hack don’t just think about how much money you might give away, but how much your customers, employees, clients and suppliers might potentially pay a scammer pretending to be you. There have been Australian cases where a business has been held liable for damages because its clients/customers have paid money to scammers posing as their business.
To learn more about how to protect yourself against cyber crime and what to do if you find yourself caught up in one, visit https://www.acorn.gov.au/


